Top 10 Smartphone Privacy Settings to Secure Your Data
Your smartphone holds a great deal of information about you, including conversations, photos, financial data, and more. That convenience is part of what makes smartphones so popular—but it also makes them a major privacy vulnerability.
Putting all of your data in one place makes it more accessible than it should be. Telecom companies, data brokers, and even cybercriminals can use this data against you. In fact, they are strongly motivated to collect and leverage this kind of data. It enables them to build accurate user profiles and predict your behaviors and preferences.
Fortunately, there are steps you can take to make your data harder to access. All modern smartphones come with data privacy settings that are genuinely useful. Most devices ship with these features switched off by default, so you’ll have to manually enable them on your own.
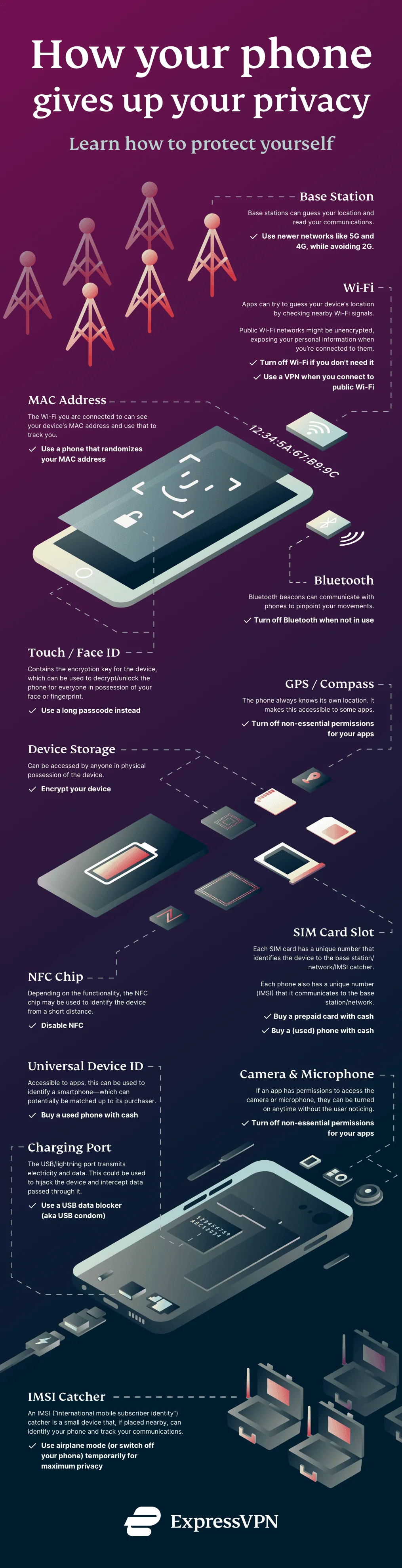
How Your Smartphone Leaks Private Data
ExpressVPN lists 13 different ways your phone hardware can leak private data about you. From using base stations to monitor user activity to recording camera and microphone data without your permission, there are many ways information about you could end up in someone else’s database:In addition to these hardware-based methods, your phone’s software applications can also divulge data about you. Many apps collect behavioral and usage data describing how and when users interact with them.
For example, a finance app may track your interest in different services it offers. If you consistently display interest in content about financing a new loan, it might categorize you as a potential customer for a finance company it is partnered with. Don’t be surprised when you start seeing ads for that company. You may even get phone calls from insistent salespeople offering you financial products.
The problem here is that the original data provider—in this case, your finance app—doesn’t always know much about its partners. A cybercriminal organization could easily pose as a finance company, purchase your intention data, and use it to target you with a loan scam. Modern AI technology significantly lowers the technical challenges of running this sort of scam, making it easier than ever to target vulnerable people
10 Smartphone Privacy Settings You Can Use to Protect Yourself
Both Android and iOS smartphones come with useful data privacy features that everyone should be familiar with. These features are typically not enabled by default, which means you’ll have to access your smartphone settings and configure them yourself. The process is not difficult, so take some time to familiarize yourself with the security features and settings you need to stay protected.
1. Limit App Permissions
Apps often request permissions beyond what they truly need. Review permissions regularly and revoke access to sensitive data like your location, contacts, and microphone unless absolutely necessary.
- On iOS, navigate to Settings > Privacy & Security.
- On Android, visit Settings > Privacy > Permission Manager.
Every app on your smartphone has its own set of permissions. These permissions control what the app can and cannot access. By managing permissions, you can decide which apps have access to your location, contacts, camera, and other data sources.
Most apps need access to certain types of data to function. For example, a weather app that doesn’t know your location may not work reliably. However, there’s no reason for the same weather app to access your contact list, camera, or microphone.
2. Disable Ad Tracking
Both iOS and Android allow users to limit ad tracking, reducing the amount of personal information advertisers can collect.
- On iOS, go to Settings > Privacy & Security > Tracking and toggle off Allow Apps to Request to Track.
- On Android, open Settings > Privacy > Ads and select Delete Advertising ID.
Advertisers want Ad tracking to seem harmless, but there are few ways to control how they use ad tracking profiles. Most profiles include behavioral patterns, shopping habits, and travel plans. That kind of data could reveal a great deal of private information about an individual.
For example, imagine you spend some time searching for vacation deals for your 10th anniversary. Anyone with access to that data could use it to infer you’ve been married for ten years. They would also know you don’t plan on being home on your anniversary date. If they correlate and enrich that information with data from other sources—like social media—they could learn even more about you.
3. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds a critical layer of security to your accounts, making it harder for unauthorized users to access your data. Enable 2FA on every app that supports it, especially ones that store sensitive information, such as messaging, banking, and email services.
Imagine a scenario where your password is compromised through a phishing attack. Without 2FA, an attacker gains immediate access. With 2FA enabled, they would still need the second verification step, significantly lowering the risk of unauthorized entry.
Using a purpose-built authenticator app is much more secure than relying on SMS authentication. The SMS network uses an old and insecure system called Signal System 7 to route messages to recipients. Exploiting this system is surprisingly easy.
4. Turn Off Location Services
Location data reveals more about your life than you might realize. Disable location services when not in use and avoid sharing your location with apps unnecessarily.
- On iOS, visit Settings > Privacy & Security > Location Services.
- On Android, go to Settings > Location.
For example, ride-hailing apps require location access when you request a ride but don't need it when the app isn't active. Protect your real-time movements by turning off location access for these apps until you need them.
5. Use Private Messaging Solutions Instead of Standard Apps
Standard messaging apps may expose your conversations to potential breaches. Opt for secure, end-to-end encrypted messaging services that prevent metadata collection and keep your interactions truly private.
End-to-end encryption ensures that only you and the intended recipient can read the messages. However, many encrypted messaging apps still collect metadata on your communication patterns. Even encrypted messaging data can reveal a great deal of information about you.
Here are just some of the things that analysis of your encrypted conversation metadata can reveal about you:
- Your sleep patterns: Nobody sends messages when they’re asleep, and many send goodnight messages to loved ones right before they go to bed.
- Your religious beliefs: Maybe you don’t contact work colleagues during religious observances, but you do reach out to friends and family in your community.
- Your social position: Celebrities and business leaders usually receive far more messages than they send. When they do send messages, people tend to respond very quickly.
6. Secure Lock Screen Settings
Ensure your device requires strong authentication for access. Use biometric options like Face ID or fingerprint scanning, along with a strong alphanumeric passcode. Disable lock screen notifications to prevent sensitive information from being visible when your phone is unattended.
Lock screen notifications can reveal sensitive information to anyone nearby. For instance, receiving a two-factor authentication code via text message could compromise your account if someone sees it over your shoulder.
7. Restrict Background Data Usage
Some apps track you even when they're not in use. Limit background data collection by going to Settings > Privacy > Background App Refresh on iOS or Settings > Network & Internet > Data Usage on Android.
Background tracking allows apps to collect information about your activity across different services. For instance, social media apps often track user behavior to refine their algorithms. Restricting background data reduces this kind of silent surveillance.
8. Turn Off Bluetooth and Wi-Fi When Not in Use
Public Wi-Fi and Bluetooth connections can be exploited to track your location or intercept data. Disable these features when not in use to minimize exposure.
Cybercriminals can exploit Bluetooth to gain access to your phone through techniques like BlueBorne. Similarly, connecting to public Wi-Fi without proper safeguards can expose sensitive data to attackers monitoring the network.
9. Regularly Audit Connected Devices and Accounts
Smartphones often remain connected to devices and services you no longer use. Check your device's settings to remove old connections and ensure only trusted devices have access.
Begin by reviewing account activity and connected devices via the account settings of major apps. Revoke access to unfamiliar or unused devices, and update passwords periodically. All of these trusted access points could become security vulnerabilities if left unmanaged.
For example, if you connect your device to a hotel Wi-Fi network, it may still retain credentials that pose a security risk. If you connect your YouTube or Netflix account to the smart TV in your room, it will remain active until you manually sign out and remove the connection. Anyone who uses the room afterwards has easy access to your account—and could use that to dig deeper.
10. Keep Software and Apps Updated
Regular updates patch security vulnerabilities that hackers can exploit. Enable automatic updates for your operating system and privacy-critical apps.
Outdated software often contains known vulnerabilities. For instance, the Pegasus spyware exploited flaws in unpatched versions of mobile operating systems to compromise devices globally. Regular updates help shield you from such threats.
Conclusion
Smartphone privacy isn't a one-time fix—it's an ongoing practice. By enabling these settings and prioritizing privacy-first tools, you can dramatically reduce your exposure to digital risks. Use these steps to take control of your personal information and prevent your data from being harvested without your knowledge.