Ransomware Prevention and Protection Strategies
Among current cyber attack types, the ransomware attack is arguably the most feared. If your system gets infected by ransomware, all your work may come to a grinding halt.
Worse, if the infected system contains your most important files, the impact of that attack will have devastating consequences.
In this article, we’ll dive into the inner workings of a ransomware attack and, more importantly, discuss the different strategies for preventing, detecting, and protecting yourself from these types of attacks.
What is ransomware and how does it work?
Ransomware is malware that encrypts files, systems, or entire networks and then notifies the victim to demand a ransom for their release.
If you pay, the ransomware operators may unlock whatever item was inaccessible. If you don't, you may lose access to those items forever.
A typical ransomware attack can be broken down into four stages:
- Infection
- Encryption (or any other method that can lock up software)
- Notification
- Ransom payment and unlocking

You can get infected through a variety of methods, including:
- Phishing – You receive an email that tricks you into either downloading an attachment (the malware itself or a trojan that downloads the ransomware) or clicking a link that takes you to a malicious site where you unknowingly download the malware.
- Drive-by-download – A harmful site that infects your system with malware by simply visiting it.
- Exploit kit – A tool that exploits software vulnerabilities to achieve malware infection.
Once the ransomware has infected your system, it starts encrypting files (or whatever it’s designed to lock up). After the encryption is complete, it displays a notification informing you that your system is locked and that you must pay a ransom to unlock it.
This notice is always displayed prominently, so you’ll know you’re infected and supposed to pay if you want to fix the problem.
Most ransomware operators demand ransom payment through cryptocurrencies, such as Bitcoin, Monero, or Ethereum, because of:
- Anonymity – It’s almost impossible to identify the owner of the crypto wallet.
- Global accessibility – You can pay ransom to practically anyone, anywhere.
- Ease of use – To pay the ransom, transactions require only a crypto wallet and a few clicks.
The most high-profile ransomware attacks in history
While ransomware attacks started gaining prominence in the early 2000s, few were more impactful and widely publicized than these:
| Event | Method of attack | Impact |
|---|---|---|
| WannaCry attack of 2017 | WannaCry, which had computer worm-like attributes, spread through networks across the globe by exploiting a vulnerability in Windows operating systems.
The operators demanded ransom payment in Bitcoin. |
Infected 200,000 computers across 150 countries. Among the most impacted were UK National Health Service (NHS) hospitals, threatening the lives of affected patients. |
| NotPetya attack of 2017 | NotPetya spread rapidly through networks using the same vulnerability exploited by WannaCry. Although now classified as a destructive wiper malware because affected computers turned out to be unrecoverable, NotPetya had ransomware malware attributes. It encrypted computer master boot records and displayed a ransom message. |
Over $10 billion in damages |
| Colonial Pipeline attack of 2021 | The perpetrators, known as the DarkSide group, used ransomware as part of a multi-stage attack. After infiltrating systems and stealing data, they unleashed their malware and demanded payment. Officials were forced to pay 75 bitcoin to restart the pipeline. |
Caused the Colonial Pipeline, which supplies nearly half of the fuel for the US East Coast, to shut down for almost a week. |
| Kaseya attack of 2021 | Ransomware-as-a-Service provider, REvil, exploited an unpatched vulnerability in Kaseya’s Virtual Systems Administrator (VSA) software, which is used by managed service providers (MSPs). This allowed REvil to distribute ransomware to organizations managed by those MSPs. |
Compromised between 800 to 1,500 organizations. |
Ransomware prevention strategies
Most types of malware try to avoid detection. Ransomware is unique in this aspect because it voluntarily reveals itself as soon as it completes encryption to obtain the ransom.
That said, it’s still important to detect an infection before the malware starts encrypting. Though antivirus software can detect ransomware infections, prevention is still the better strategy.
It’s challenging to detect a ransomware infection, as many variants employ evasive tactics. Also, once ransomware has established a beachhead in your system, it doesn’t take much time to complete the encryption process.Some ransomware variants, like LockBit, can encrypt 25,000 files per minute.
To effectively prevent ransomware, you can focus on preventive measures, such as:

- Keep your systems and applications updated – Ransomware usually exploits software vulnerabilities to gain a foothold. Many software updates include security patches, so updating your software dramatically reduces the risk of a ransomware infection.
- Implement anti-phishing strategies – Cybercriminals can distribute ransomware through phishing emails, making anti-phishing strategies, like not clicking links or downloading attachments in suspicious emails, effective against ransomware.
- Install antivirus or anti-malware tools – Just as they can detect the presence of malware, some antivirus tools can also block potential ransomware infections. Reputable tools like Bitdefender, ZoneAlarm, Sophos Home, and NeuShield are known to be effective against specific ransomware variants.
- Institute regular backups – While backups won’t prevent a ransomware infection, they will substantially reduce the impact of a ransomware attack. If you have backups of your files, you can simply revert to those backups if you fall prey to a ransomware attack.
How to respond to a ransomware attack
While preventive measures can help against ransomware, none are foolproof. So, what if ransomware manages to slip through? Here are some helpful tips.

- Isolate the infected device – Ransomware can spread to other devices. To prevent this, disconnect the infected device from your home or office network along with any external storage devices.
- Assess the situation – Determine what parts of your system are affected. Is it your entire system? Is it just specific files? Find out if you can access any of your essential files. If you still can, copy them to an external drive. Gather enough information (see Step 3) before planning your next course of action.
- Find out more about the ransomware – Google or ChatGPT the exact message displayed on the ransom note. Chances are, you’ll find information describing the characteristics of the ransomware in question. You’ll know, for instance, if it encrypts your entire system or just certain files. Better yet, you might find a way to resolve the issue.
- Attempt recovery without paying ransom – If you have backups of the affected files, you’re safe. Just format the affected system and reinstall everything. If you don’t have backups, see if you can find a decryption tool for the ransomware in question at https://www.nomoreransom.org.
- Seek professional help – If all fails, you can find several service providers online that offer ransomware remediation services. Here are some of them:
Ransomware trends you need to be aware of
Tracking ransomware trends can help you assess whether specific threats remain significant or if new threats require more focus.
Here are some trends related to ransomware.
Most financially motivated attacks use ransomware and other extortion-based attacks
From the latter part of 2021 until 2024, most financially motivated threat actors have been using ransomware and other extortion-based attacks. These types of attacks have accounted for a minimum of 59% to a maximum of 66% of all financially motivated attacks over the said period.
These attacks give those threat actors the best return on investment, so they won’t be going away soon.
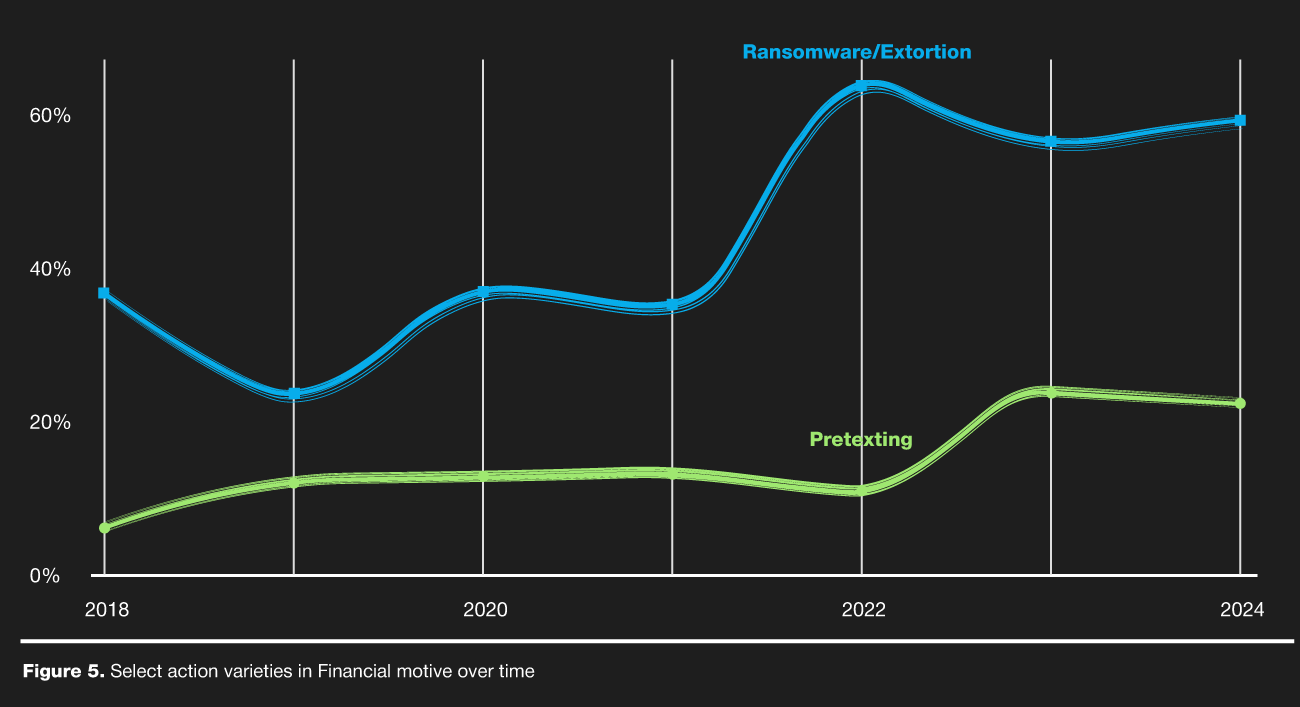 Chart created by OffGrid, data sourced from Verizon 2024 Data Breach Investigations Report
Chart created by OffGrid, data sourced from Verizon 2024 Data Breach Investigations Report
Growing interest in AI-powered ransomware
In December 2024, a newly emerged ransomware group, FunkSec, quickly became the most active player in cybercrime, claiming over 85 victims in a single month. What sets FunkSec apart is its use of artificial intelligence (AI) in malware development, marking a new trend in ransomware.
As AI-driven threats gain traction, a quick look at Google Trends confirms the growing interest in this evolving cyber threat.
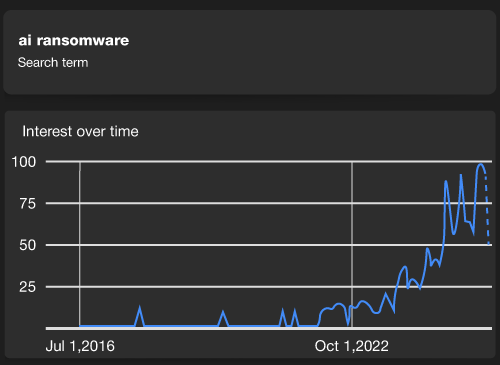
Chart created by OffGrid, data sourced from Google Trends
Conclusion
Ransomware remains one of the most severe cyber threats, capable of crippling individuals, businesses, and critical infrastructure. As attackers now leverage AI to enhance their malware, the threat is increasing.
However, you can significantly reduce your risk by adopting a proactive approach.
Prevention is your first line of defense. You should keep systems updated, implement anti-phishing measures, and maintain regular backups. Detection tools and antivirus software can help, but staying informed and vigilant is equally crucial.
If an attack occurs, you can isolate the infected device, assess the situation, and explore recovery options before considering ransom payments.
The best defense against ransomware is a combination of technology, awareness, and swift action.
